Intelligent Workplace Connectivity
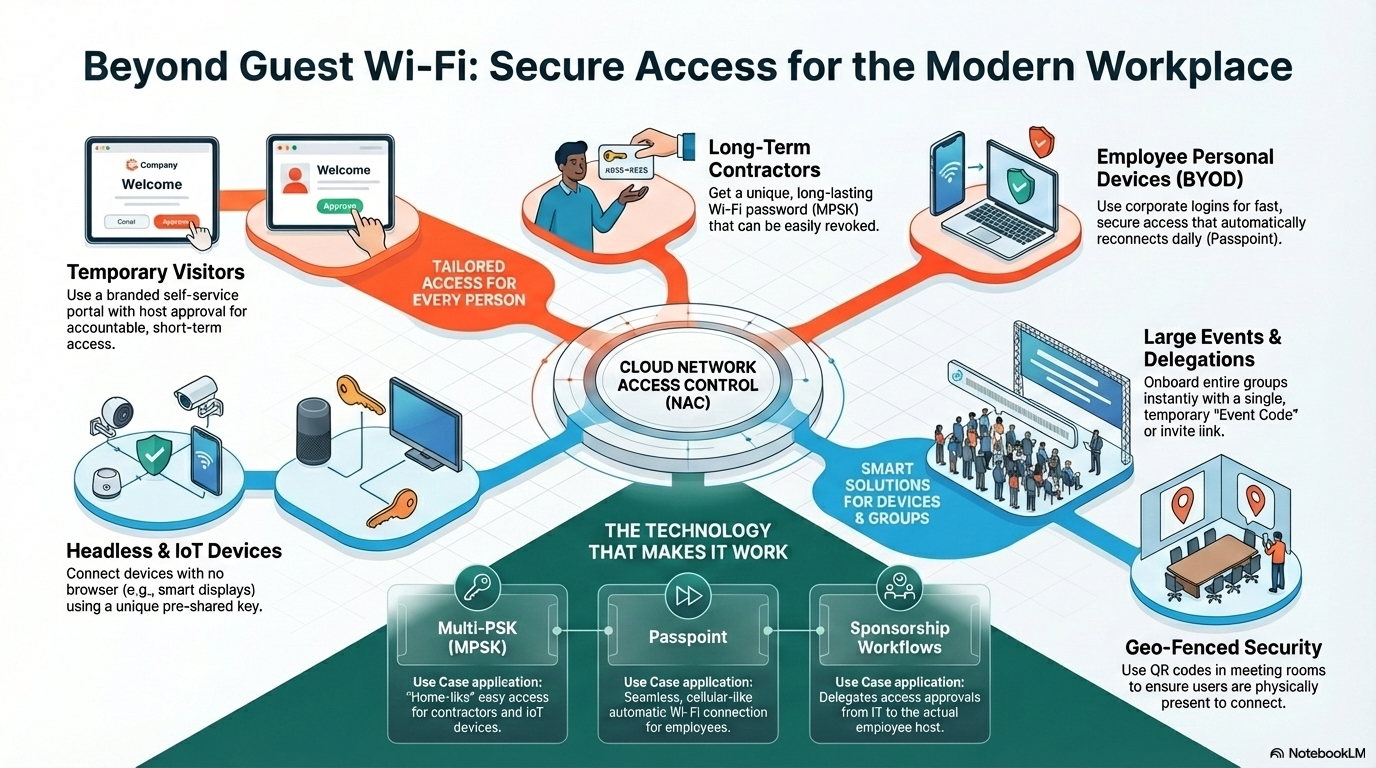
Orchestrate secure, seamless access for every user type—visitors, contractors, BYOD, and IoT—using Flexible Cloud NAC and Multi-PSK technology.
Deep Dive
The modern corporate office is a hub of transient activity. From daily visitors and cleaning crews to VIP delegations and employee personal devices, the "one-password-fits-all" approach to Guest Wi-Fi is dead. It creates security holes and frustrates users.
The Solution: User-Centric Access Model
We break down how a Cloud NAC solution addresses specific scenarios by User Persona:
A. The Temporary Visitor (Meetings & Showcases)
B. The Contractor & Long-Term Partner
C. The Employee (BYOD & Personal Devices)
D. Events & Delegations (Bulk Onboarding)
E. Headless & Medical Devices (IoT)
Feature Spotlight:
Zero-Touch IT
Self-service portals and sponsorship offload work from the helpdesk. No more tickets for Wi-Fi passwords.
Granular Security
Employees get high-speed/unlimited access; guests get internet-only access; IoT gets isolated access—all on the same infrastructure.
Compliance & Audit
Full audit trails of exactly who is on the network, who sponsored them, and when their access expires.
The Challenge
Managing different security policies for a CEO’s iPad, a cleaning contractor’s phone, and a visitor’s laptop is manually impossible. Strict security often means poor user experience (UX), while 'open' networks create massive liabilities.
Solution Engineering
A Flexible Cloud NAC solution. It orchestrates secure, seamless access for every type of user. By leveraging technologies like Multi-PSK (MPSK), Passpoint, and dynamic Captive Portals, it ensures security never comes at the expense of the user experience.
Technical Requirements
- Cloud NAC Policy Engine
- Multi-PSK (MPSK) / iPSK Capability
- Passpoint / Hotspot 2.0 Support
- Sponsorship Workflow (Email/Slack/Teams)
- Dynamic VLAN Assignment
Best Practices
Enable 'Sponsor Approval' for anyone needing access to internal resources.
Use Multi-PSK for contractors with a set expiration date (e.g., 30 days).
Implement physical QR codes in meeting rooms to bind access to location.
Isolate IoT/Headless devices on separate VLANs using unique MPSK keys.
Target Outcomes
Zero Trust Security posture for visitors
Auditable access logs for compliance (ISO 27001)
Reduced IT Helpdesk tickets for WiFi passwords
Frequently Asked Questions
Multi-PSK allows multiple different passwords to work on the same Wi-Fi SSID. Each password is tied to a specific user or device profile, allowing IT to revoke one specific device without changing the password for everyone else.
When a guest registers on the portal, they enter their host's email. The host receives a one-click approval link via Email, Slack, or Teams. Access is granted only after the host clicks 'Approve'.
Recommended Vendors
Companies matching this use case based on their feature set.

Cloud4Wi
Unified WiFi platform for Guest, MDU & Location Intelligence.

Tanaza
Leading Public Facing Guest solution for Retail.

Ucopia
Leading Public Facing Guest solution for Healthcare.

Aptilo (Enea)
Leading Public Facing Guest solution for Transportation.

Aruba Networks
Leading Corporate Guest solution for Enterprise Office.

Cisco Meraki
Leading Network Access Control solution for Enterprise Office.

Juniper Mist
Leading Network Access Control solution for Enterprise Office.

Extreme Networks
Leading Network Access Control solution for Large Venues.