The Network Engineer’s Guide to DMCA Forensics: NAT, Logs, and Identity Correlation in Higher Ed
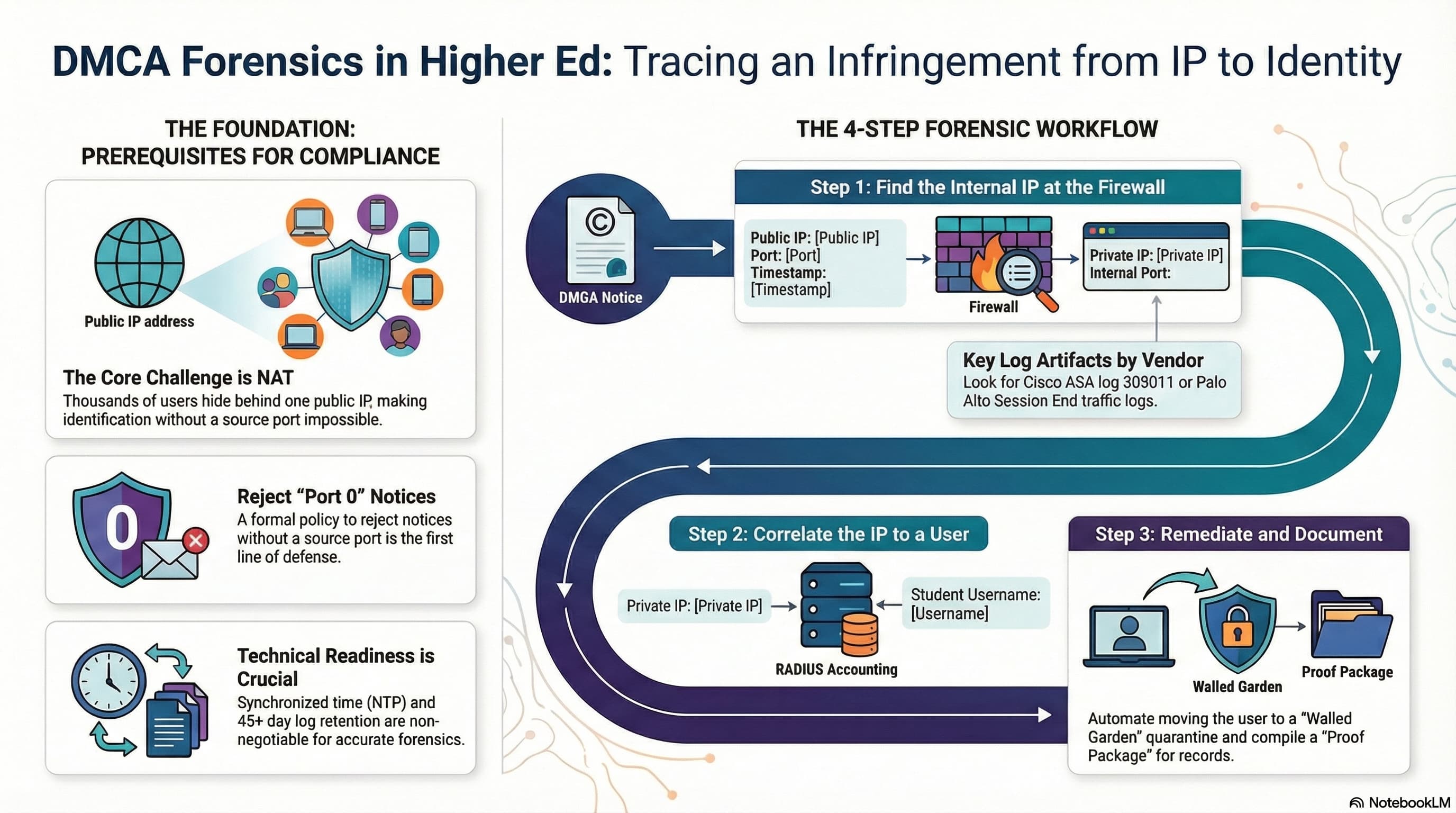
Executive Summary: In the landscape of US Higher Education, the IT department is not merely a utility provider; it is the primary guardian against institutional liability. This guide moves beyond policy to detail the forensic workflows required to translate a DMCA violation notice (often just an IP and timestamp) into a verifiable user identity within a complex, Network Address Translated (NAT) campus environment.
2. The Technical Barrier: Why DMCA Processing is Hard
The primary challenge in DMCA investigations is Network Address Translation (NAT), specifically PAT (Port Address Translation). In an era of IPv4 exhaustion, thousands of students often hide behind a single public IP address.
✕ The "Port 0" Issue
Without the specific source port used at the exact millisecond of the infringement, it is mathematically impossible to distinguish one student from another in a PAT environment. If a notice arrives with "Port 0", reject it immediately.
✓ The Clock Imperative
Network Time Protocol (NTP) must be synchronized across Firewalls, NACs, and Syslog servers. A drift of even a few minutes can lead to false positives.
3. Phase 1: Perimeter Investigation (Traversing the NAT)
The first step is to map the Public IP/Port provided in the notice to an Internal Private IP. The methodology varies by firewall vendor.
Vendor Cisco ASA and Firepower (FTD)
Standard connection logging is often too noisy. You must enable specific NAT logging using Syslog ID %ASA-6-305011 ("Built Translation").
logging list DMCA-Tracking message 305011
logging trap DMCA-Tracking
Vendor Palo Alto Networks (PAN-OS)
Palo Alto firewalls log at the "Session" level. Search for logs where the nat_source_ip and nat_source_port match the notice. Caveat: Since P2P sessions are long-lived, search for logs where the Start Time is before the notice timestamp and the Generate Time is after.
4. Phase 2: Identity Correlation (Mapping IP to User)
Once you have the Internal IP, you must identify who was using it. This data resides in the AAA layer. Authentication logs often lack IP info, so you must rely on Accounting Logs.
Configuration Requirement: Enable Interim Accounting (e.g., every 10-15 minutes) on your WLC. This forces the WLC to update the RADIUS server with the user's IP address once DHCP is complete.
Cisco ISE
Go to Operations > Reports > Endpoints and Users > RADIUS Accounting. Filter by Framed-IP-Address.
Aruba ClearPass
Navigate to Monitoring > Live Monitoring > Accounting. Use the filter Framed-IP-Address CONTAINS [Private IP].
5. Phase 3: Remediation and Enforcement
To satisfy the HEOA requirement to "effectively combat" infringement, institutions typically use a "Walled Garden" approach.
-
The Architecture A dedicated quarantine VLAN (e.g., VLAN 666) with ACLs that deny all internet access except for DNS, DHCP, and traffic to a remediation portal.
-
Automated CoA Modern NACs can automate this. In Cisco ISE, create an ANC Policy marked QUARANTINE and issue a CoA Re-Auth to instantly bump the user into the Walled Garden.
6. Data Governance: Log Retention Strategy
| Log Type | Retention Period | Reasoning |
|---|---|---|
| NAT/Firewall Logs | 45 - 90 Days | DMCA notices often lag by 7-14 days. 45 days provides a safety buffer. |
| RADIUS/NAC Logs | 180 Days | Valuable for general security forensics beyond DMCA. |
| Case Files | 7 Years | Retain the "Proof Package" to satisfy institutional record-keeping policies. |
Need help auditing your logging strategy?
Ensure your institution is Safe Harbor compliant with a comprehensive network observability audit.
Contact Our Engineering Team →Was this guide helpful?
Speak to an Expert